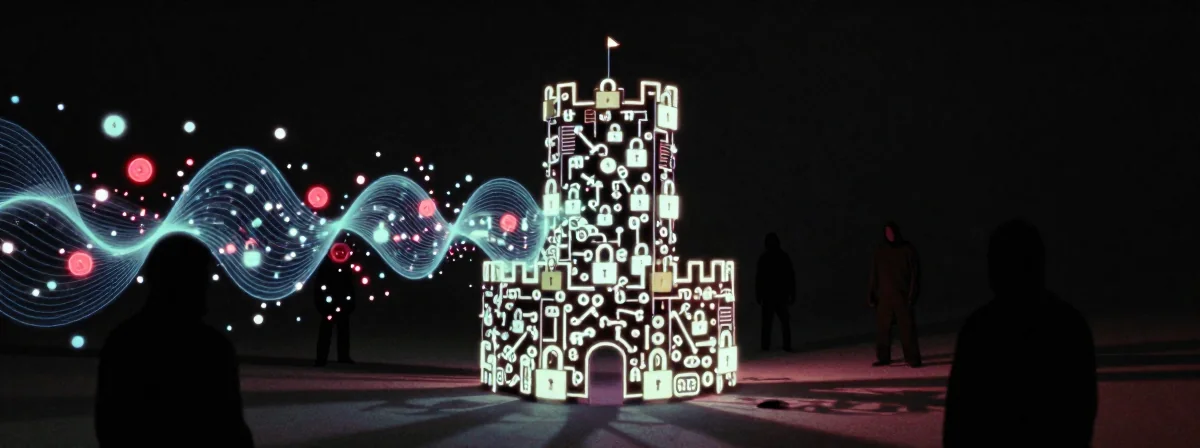
Imagine you’re playing a game where the rules change mid-match—except this time, the rulebook is being rewritten by quantum physics. Your current encryption might feel like a fortress, but what if the locks can be picked by machines that don’t exist yet? That’s the quantum threat lurking in the shadows, and it’s more immediate than you think.
Most discussions about quantum computing focus on sci-fi fantasies or distant futures. But the real danger isn’t about what quantum computers can do today—it’s about what they’ll do tomorrow to data captured today. Think of it like a hacker recording every move you make now, waiting for the right tools to crack your defenses later. That’s the quantum threat in a nutshell.
The truth is, quantum computers capable of breaking modern encryption don’t exist yet. But the seeds of their power are already planted, and the clock is ticking. Here’s what you need to know.
Will Your Encryption Hold Up Against Future Quantum Attacks?
The short answer: probably not, unless you’re already ahead of the curve. Modern encryption relies on problems that are computationally hard for classical computers—like factoring large numbers. Quantum computers, hypothetically, could solve these problems efficiently using Shor’s algorithm. It’s like upgrading from a lockpick to a master key that works on every lock.
But here’s the twist: no one is safe from future threats by default. If an adversary records encrypted traffic today, they could store it until quantum computers mature. Then, they’d have a time machine for decryption. This isn’t science fiction—it’s a documented concern in cybersecurity circles. It’s the ultimate “save now, crack later” strategy.
The analogy here is like building a house with locks that work today but might be obsolete tomorrow. You wouldn’t blame the locksmith for future key designs, but you’d be foolish not to plan ahead.
Are Quantum Computers a Real Threat Right Now?
Not in the way you might imagine. The quantum computers we have today are more like prototypes than production models. They struggle with stability, error rates, and scale. It’s like having a car engine that can theoretically reach 300 mph but can only run for 10 seconds at a time.
This doesn’t mean the threat is imaginary—it just means the window for preparation is open. The real danger isn’t today’s quantum computers; it’s tomorrow’s. Just as early computers were laughably weak by today’s standards, today’s quantum machines are just the first level of a much larger game.
The counterintuitive point? The time to act is now, even though the threat isn’t immediate. It’s like preparing for a blizzard in the summer—because by the time winter hits, it’s too late.
What About Performance Impacts? Does Quantum Encryption Slow Things Down?
Here’s where most people get it wrong. The idea that quantum-resistant encryption will grind your systems to a halt is a myth—mostly. The performance hit comes from using hybrid encryption, where you wrap a fast, symmetric key (like AES) with a slow, quantum-resistant key.
But guess what? High-performance systems already do this. They use asymmetric encryption only for key exchange, then switch to symmetric encryption for the actual data. It’s like using a helicopter to deliver a key, then a sports car to transport the goods. The hybrid approach isn’t new—it’s just becoming a necessity.
The unexpected insight? If your system can’t handle this hybrid approach now, it’s already poorly optimized. Performance-critical applications have been doing this for years. The real cost isn’t in speed; it’s in the complexity of implementation.
How Can You Future-Proof Your Encryption Today?
The solution isn’t magic—it’s foresight. Post-quantum cryptography (PQC) algorithms are being standardized now, and some are already in use. NIST’s PQC competition isn’t just a research project; it’s the blueprint for the next generation of encryption.
Think of it like upgrading from dial-up to fiber-optic internet. The technology existed before you needed it, but waiting until everyone else was already online would leave you in the dust. The same applies here. Migrating to PQC now means you won’t be caught scrambling when quantum computers finally arrive.
The specific detail? Some financial institutions and government agencies are already testing PQC in non-critical systems. It’s like a fire drill—practicing before the real emergency.
What If You Can’t Afford to Upgrade Now?
The good news is you don’t have to rip out everything at once. Start with the most sensitive data. Use PQC for long-term storage or critical communications. It’s like reinforcing the doors to your vault before you worry about the windows.
The analogy here is game development: you don’t optimize everything at once. You identify bottlenecks and fix them first. Similarly, identify your most vulnerable data paths and secure them with PQC. The rest can follow later.
The Single Idea That Changes Everything
Here’s the reframing: quantum computing isn’t a distant threat; it’s a ticking clock. The data you encrypt today could be decrypted tomorrow by machines we’re building now. The only defense isn’t better locks—it’s planning for the inevitable.
It’s like preparing for a game where the rules will change. You don’t win by ignoring the rulebook; you win by understanding it before the game starts. Quantum computing is that rule change, and the time to read the new rules is now.